top of page
Insights
Practical security analysis for organizations operating in high-risk environments.


The Gulf's Procurement Paradox: Why Heavy Defense Spending Did Not Translate into Defensive Resilience
(Creator: Amr Alfiky | Credit: REUTERS) When the Islamic Republic of Iran initiated its retaliatory air campaign against Gulf Cooperation Council (GCC) states on 28 February 2026, the early performance metrics suggested a vindication of two decades of regional defense investment. The United Arab Emirates' Ministry of Defence reported the interception of more than 530 ballistic missiles and over 2,200 one-way attack drones during the campaign's first six weeks, with reported G


Hormuz, Pharma Supply Chains, and the BCP Gap
The Scene Nobody Connected A pharmacist in Germantown, Ohio fills prescriptions on a Tuesday morning. Shelves are stocked. Business is normal. Half a world away, 230 oil tankers sit stranded in the Persian Gulf, unable to move. These two scenes look unrelated. They are not. On February 28, 2026, the United States and Israel launched coordinated airstrikes on Iran under Operation Epic Fury. Within days, Iran responded by effectively closing the Strait of Hormuz — the narrow wa


Why Our Risk Radar Might Be Blinded— and How to Sharpen It
We all believe we can spot danger before it strikes—until we realize that our methods for judging risk are often flawed. Let’s fix that. What Is Risk? In professional fields, risk is typically defined as likelihood × impact —a helpful formula for estimating how probable an event is and how severe its consequences might be. Essentially, during risk assessment, you assign a number to both the likelihood and the impact across different scenarios to guide decisions. ISACA Why We

From Past to Prediction: Why Context Must Reshape Modern Risk Assessment
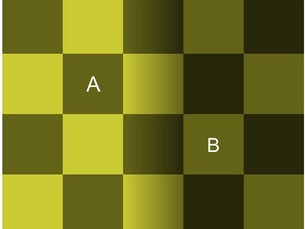
At first glance, two squares on a chessboard seem completely different in color. But place them in a different context, and you realize they’re exactly the same. Our eyes were tricked by the surroundings. Risk assessments work much the same way — without context, what we think we “see” is often misleading. And just like the illusion, the consequences of misreading reality can be serious. In contemporary security practice, risk assessment is often portrayed as a rational, data


Intelligence Failure or Decision-Maker Misjudgment?
When we think of intelligence failure, we often focus on the intelligence cycle itself—collection, analysis, assessment, and dissemination. This cycle isn’t complete without feedback from the decision-maker to the intelligence apparatus, closing the loop. The implication here is straightforward: if a failure occurs at any stage—whether during collection, analysis, or dissemination—it falls under the umbrella of an intelligence failure. However, things get murky when issues ar


The Importance of Establishing an Accurate Timeline in Security Risk Assessments
When conducting a security risk assessment, one of the most critical yet often overlooked elements is defining the timeline of the assessment. Is the assessment aimed at risks over the next two weeks, six months, or the next five years? The answer fundamentally shapes the outcome. In humanitarian work, where organizations operate in volatile regions like the Middle East, an accurate timeline can spell the difference between a plan that protects staff and assets effectively an
bottom of page